Remove HP bloatware on Windows 10
Welcome to another part of the "Remove bloatware" series. 😁
As you have read in the previous blog post, we still had to deal with the HP bloatware that was still present on the devices.
Since my test laptop was already connected to Intune, I could use the Endpoint Manager portal at the devices Discovered apps blade to see the exact description of the installed HP software. Just search for HP and problably you will get a list of installed HP software. But HP also installs Appx applications, and they all start with AD2F1837.packagename.
So, I grabbed the script of mark05E again and edited it to our needs and also created a detection file. Basically the same as with the Windows 10 bloatware remover script. However, in addition to the Appx packages, there are also the "normal" installed apps.
I edited the script for this specific task to remove the HP bloatware.
First a tag file, RemoveHPBloatware.ps1.tag, for detection in Intune, so that Intune sees that it is installed and of course a log file, RemoveHPBloatware.log, to check afterwards whether the script has also worked.
# Create a tag file just so Intune knows this was installed
if (-not (Test-Path "$($env:ProgramData)\HP\RemoveHPBloatware"))
{
Mkdir "$($env:ProgramData)\HP\RemoveHPBloatware"
}
Set-Content -Path "$($env:ProgramData)\HP\RemoveHPBloatware\RemoveHPBloatware.ps1.tag" -Value "Installed"
# Start logging
Start-Transcript "$($env:ProgramData)\HP\RemoveHPBloatware\RemoveHPBloatware.log"
Second part of the script is to add the HP Appx packages in the script. Ofcourse you can add or remove packages from this list.
# List of built-in apps to remove
$UninstallPackages = @(
"AD2F1837.HPEasyClean"
"AD2F1837.HPPCHardwareDiagnosticsWindows"
"AD2F1837.HPPowerManager"
"AD2F1837.HPPrivacySettings"
"AD2F1837.HPProgrammableKey"
"AD2F1837.HPQuickDrop"
"AD2F1837.HPSupportAssistant"
"AD2F1837.HPSystemInformation"
"AD2F1837.HPWorkWell"
"AD2F1837.myHP"
"Tile.TileWindowsApplication"
)
Third part of the script is to add the HP installed programs. Again, you can add or remove software from this list.
# List of programs to uninstall
$UninstallPrograms = @(
"HP Client Security Manager"
"HP Notifications"
"HP Security Update Service"
"HP System Default Settings"
"HP Wolf Security"
"HP Wolf Security Application Support for Sure Sense"
"HP Wolf Security Application Support for Windows"
)
$HPidentifier = "AD2F1837"
The rest of the script is the same, so we don't need to change anything there.
Now we can deploy it via Microsoft Intune. In my GitHub repository, you will find the .ps1 and an intunewin file. You can download both, if you are satisfied with the removal of the earlier mentioned built-in apps. 😁
If not, then you need to edit the script and wrap it to an intunewin file. But I think that you know how to do that.
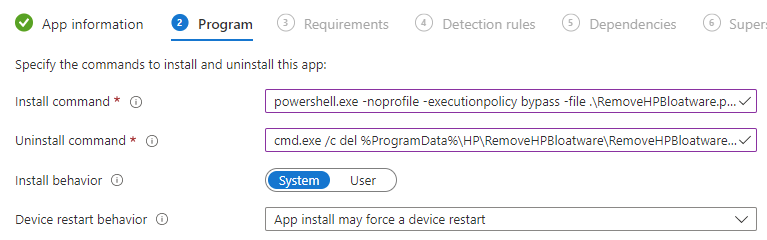
To deploy this with Intune, we need to use the following settings at the Programs tab:
-
At the Install command field, type this:
powershell.exe -noprofile -executionpolicy bypass -file .\RemoveHPBloatware.ps1 -
At the Uninstall command field, type this:
cmd.exe /c del %ProgramData%\HP\RemoveHPBloatware\RemoveHPBloatware.ps1.tag
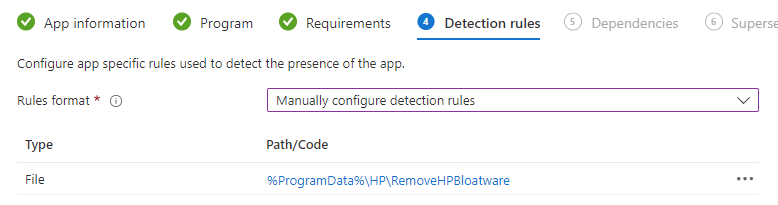
And we need to use the following settings at the Detection rules tab.
- From the Rules format dropdown, select Manually configure detection rules
- Click on + Add
- At the Rule type dropdown, select File
- In the Path field, type
%ProgramData%\HP\RemoveHPBloatware - In the File or folder field, type
RemoveHPBloatware.ps1.tag - From the Detection method dropdown, select File or folder exist
- Click on OK
You need to assign this application to your HP devices, via an Azure AD group. Dynamically or static, or you can use the Filters options, nowadays.
And now we have to wait for the program has been arrived on your targeted systems. A few minutes later, after the script has done his work, you will see that the apps, mentioned in the script, are removed from your Windows 10 device.
Thanks for reading and see you next time.